Executive Summary:
This step-by-step implementation guide offers helpful ideas for utilizing the power of face detection to boost security, improve customer experiences, and expedite various corporate procedures.
Introduction:
Face detection technology has revolutionized how businesses operate, providing a wide range of applications that enable personalized client interactions and improve security and access management. Face identification software can be a big step towards increasing business efficiency and offering better services.
This blog provides a step-by-step implementation manual to assist organizations in implementing face detection into their workflows.
Face Detection Solution: An Overview
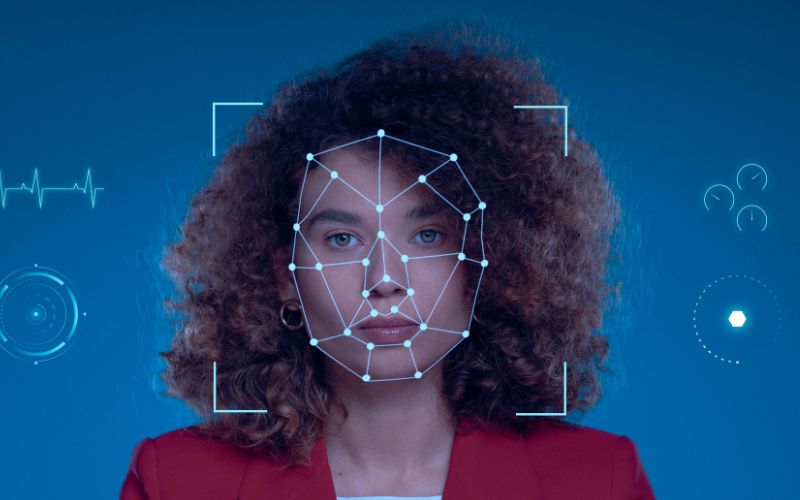
Many facial recognition systems are built on sophisticated computer vision technology known as face detection. Computers can reliably recognize and analyze facial features thanks to the automatic recognition and localization of human faces in pictures and videos.
For businesses wishing to utilize face detection technology successfully, it is crucial to comprehend the components and operating theories of a face detection solution.
Evaluating Business Goals and Needs:
Businesses must carefully evaluate their unique needs and goals before using any technology, including face detection technologies. This first stage lays the groundwork for a successful deployment by ensuring that the technology aligns with the company’s strategic objectives and answers its most pressing problems.
The procedure for determining business needs and goals is explained in detail here:
- Finding Obstacles:
Businesses must first define the problems and issues that face detection solution is intended to solve. This could involve compliance, customer satisfaction, operational effectiveness, or security concerns. Examining how face detection can offer answers requires a good understanding of these problems.
- Setting Objectives:
After identifying their pain points, businesses should create specific, quantifiable goals for face detection deployment. The goals might include things like improving security through facial recognition access control, personalizing client interactions, improving attendance tracking, or lowering fraud in online transactions, for example.
Setting objectives aids in establishing reasonable standards and benchmarks for gauging the effectiveness of the technology.
Choosing the Best Hardware for Face Recognition:
A crucial stage in the effective implementation of face detection technology is choosing the right hardware. Face detection is accurate and effective with the correct hardware, allowing businesses to accomplish their goals successfully.
- Establish Specific Requirements:
Businesses must ascertain their unique face detection needs before looking into hardware choices. Think about things like the system’s intended use, the number of cameras required, the location in which it will function, and the anticipated volume of faces that will be recognized simultaneously.
Knowing these specifications will make choosing hardware that supports the company’s objectives easier.
- Camera Resolution and Type:
The effectiveness and accuracy of face detection are highly dependent on the type of camera used. Businesses have various camera options, including IP cameras, 3D cameras, and specialized facial recognition equipment. Each type of camera has benefits and drawbacks.
Selecting the Right Face Detection Method:
The success of the technology’s application is greatly influenced by choosing the best face-detection solution. Businesses must carefully evaluate their needs and goals to choose the best face detection solution from the market’s options.
- Precision and Effectiveness:
Important things to think about are the face detection solution’s performance and accuracy. More reliable detection is ensured by higher accuracy, which reduces false positives and negatives.
Be sure to choose solutions that have undergone extensive testing and review to confirm their correctness under various circumstances, such as lighting, angles, and facial expressions.
- Instantaneous Processing:
Make sure the chosen face detection solution can process data fast for applications that need real-time face detection, such as access control or surveillance. Real-time processing is necessary for quick replies and actions based on recognized faces.
Ensuring Privacy and Compliance of Data in Face Detection:
Face detection includes managing delicate biometric data; therefore, protecting data privacy and adhering to applicable laws is crucial. To preserve customer privacy and follow data protection rules, businesses must follow extensive procedures.
- Rules for Data Protection:
Learn about the data protection laws that apply to your community and profession. The General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and comparable laws in other nations are examples of common regulations.
Ensure that your face detection system complies with the laws that apply to collecting, processing, and storing biometric data.
- Encryption and Anonymization:
Use effective data anonymization and encryption methods to safeguard the security and privacy of biometric data. While encryption ensures that the data is still unreadable to unauthorized parties, anonymization ensures that no personally identifying information is left in the data.
Implementing the Face Detection Hardware Setup:
Implementing the hardware setup is one of the most important steps in effectively deploying a face detection system. The hardware configuration creates the groundwork for precise and dependable face identification, allowing enterprises to accomplish their goals successfully.
- Careful camera positioning:
Plan carefully and install cameras strategically to achieve the best face detection results. Recognize crucial locations, such as entry points, customer service stations, or high-traffic regions, where face detection is necessary.
Consider variables like illumination, angles, and distances to guarantee that the cameras record clean and unobstructed facial photos.
- Camera Calibration:
To ensure dependable operation and precise measurements, calibrate the cameras. Camera calibration entails altering camera settings, including focus, exposure, and white balance, to produce the best possible images.
Accurate calibration enhances face detection performance, particularly in various lighting situations.
Adding Face Detection to Existing Systems:
A critical step in maximizing the advantages of this technology for enterprises is the integration of face detection with current systems. The fast interchange of data, improved workflows, and improved functionality across numerous processes are all made possible by seamless integration.
- Determine the Points of Integration
Start by determining the precise integration points where face detection will be valuable in your current systems. Access control systems, customer relationship management (CRM) software, attendance tracking systems, and security surveillance networks are examples of common interaction points.
- Select Compatibility in Solutions:
Pick a face detection method that works with your current setup. Check whether the face detection program has APIs (Application Programming Interfaces) or SDKs (Software Development Kits) that enable simple integration with other software programs and platforms.
Face detection system maintenance and monitoring:
To manage a face detection system efficiently, monitoring and maintenance are crucial. While preventive maintenance helps prevent problems and preserves the system’s longevity, regular monitoring ensures the system runs as efficiently as possible.
- Real-time Observation:
Implement continuous performance tracking of the face detection system in real-time. Monitoring tools can reveal information on the precision of face detection, the responsiveness of the system, and resource usage. Administrators can set up alerts to inform them of any potential problems or abnormalities.
- Data Quality Control:
Check the accuracy of the system’s acquired facial data. To maintain precise face detection, ensure that photographs are of a sufficient resolution, well-lit, and unobstructed. Find and fix any image quality problems affecting the system’s performance.
Conclusion:
Deploying face detection software has revolutionized several industries, changing how companies run and interact with their clients. Face detection solution has several advantages, from enhancing security and increasing operational effectiveness to delivering individualized client experiences, as this blog has illustrated.
Businesses may use the potential of this cutting-edge technology to meet their specific needs and goals by understanding the power of face detection technologies.
Face identification improves attendance tracking, analyses consumer behavior, and reliably identifies people for access control, among other operations, unlocks new growth opportunities.
Frequently Asked Questions (FAQs)
Q) What advantages can face recognition offer businesses?
A) Face detection makes Access control and surveillance possible, improving security. Additionally, it increases operational effectiveness, provides personalized customer service, makes attendance tracking and customer analytics easier, and more.
Q) How does face recognition operate?
A) Face identification algorithms examine visual patterns and photo features to find areas likely to have faces. The algorithms use the sliding window approach, feature extraction, and classification to identify and detect faces accurately.
Q) Is facial recognition similar to face detection?
A) facial recognition recognizes general people, but face detection locates faces in photos.
Q) How can companies ensure that data privacy requirements are followed?
A) To comply with data privacy legislation, businesses should adhere to best practices, get consent, and give priority to security measures.
Q) Is facial detection a viable access control method?
A) it is frequently used for security and access control applications.